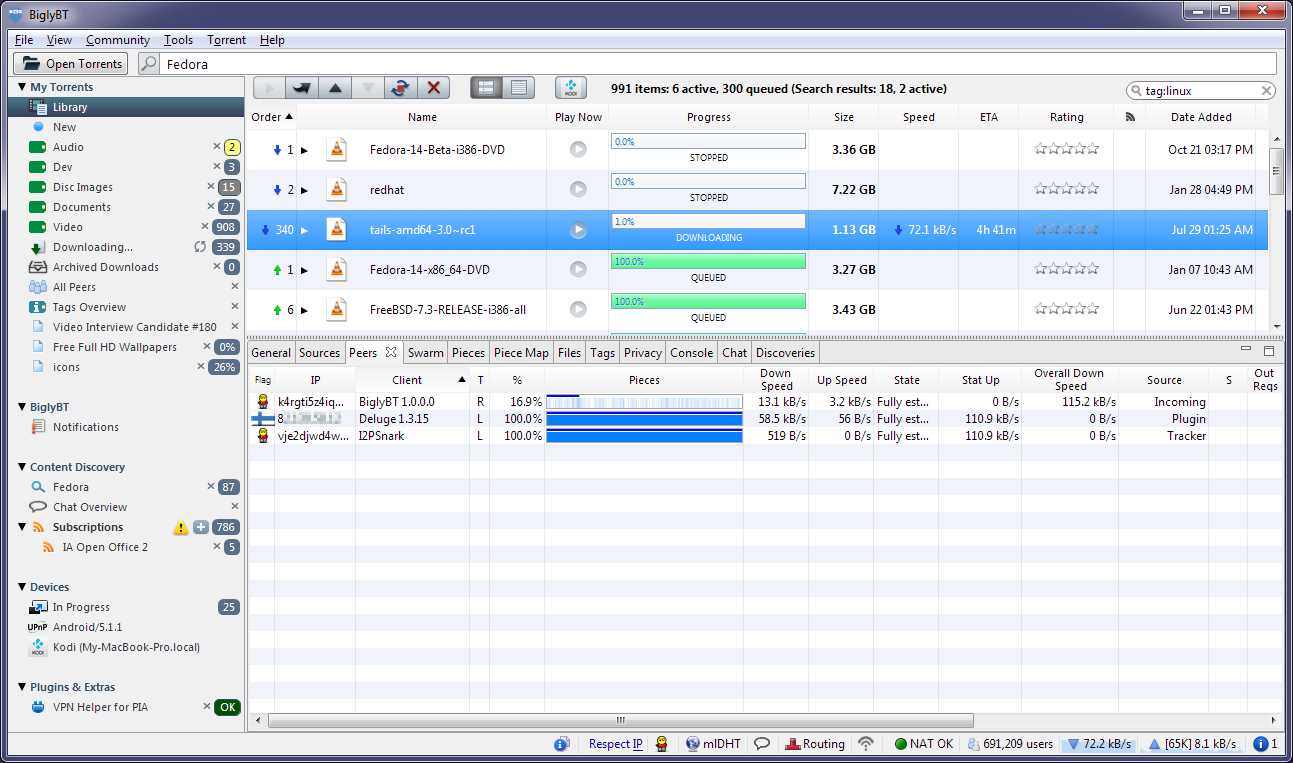
I wouldn't go as far as saying it isn't possible - I'm running ~30 services for a combined ~110 tunnels on my router. But you would definitely want to do some kind of tunnel management if you were spinning up one Destination per site. I would suggest dropping to one or two inbound and outbound tunnels each for low load (probably dropping down to only one for sites that have no peers downloading for some time), and adding more as load increases. Vuze uses a similar mechanism to great effect (I've had as much as 200kB/s combined download speed for torrents over I2P, at which point Vuze will have IIRC six inbound and outbound tunnels).
Introduction to I2P. Overview of comparisons. The I2P network provides strong privacy protections for communication over the.
One downside to this mechanism would be that it becomes easy to determine which sites are popular, by observing which ZeroNet Destinations have more tunnels. But maybe this isn't part of your threat model.
The setup Vuze uses is to have only two Destinations: one for torrents that it seeds inside I2P only, and the other for torrents that it simultaneously seeds on the public internet. This minimizes correlation between their public and anonymous activity.
| Original author(s) | I2P Team[1] |
|---|---|
| Initial release | 2003; 16 years ago |
| Stable release | |
| Repository | |
| Written in | Java |
| Operating system | Cross-platform |
| Available in | English, Spanish Incomplete translations: Russian, French,Romanian, German, Swedish, Italian, Portuguese, Chinese, Dutch, Polish, Hungarian, Arabic, Japanese, Estonian, Persian[3] |
| Type | Overlay network |
| License | Free/Open Source – different licenses for different parts[4]Public domain, BSD, GPL, MIT |
| Website | https://geti2p.net, https://geti2p.net/fr/, https://geti2p.net/de/, https://geti2p.net/ru/ |
The Invisible Internet Project (I2P) is an anonymous network layer (implemented as a Mix Network) that allows for censorship-resistant, peer to peer communication. Anonymous connections are achieved by encrypting the user's traffic (by using end-to-end encryption), and sending it through a volunteer-run network of roughly 55,000 computers distributed around the world. Given the high number of possible paths the traffic can transit, a third party watching a full connection is unlikely. The software that implements this layer is called an 'I2P router', and a computer running I2P is called an 'I2P node'. I2P is free and open source, and is published under multiple licenses.
- 1Technical design
- 2Software
- 2.3File sharing
- 6See also
I2p Torrent
Technical design[edit]
I2P is beta software since 2003.[5] The software's developers emphasize that there are likely to be bugs in the beta version and that there has been insufficient peer review to date.[6] However, they believe the code is now reasonably stable and well-developed, and more exposure can help development of I2P.
The network itself is strictly message-based (like IP), but there is a library available to allow reliable streaming communication on top of it (similar to TCP, although from version 0.6 there is a new UDP-based SSU transport). All communication is end-to-end encrypted (in total there are four layers of encryption used when sending a message) through garlic routing,[7] and even the end points ('destinations') are cryptographic identifiers (essentially a pair of public keys), so that neither sender nor recipient of a message need to reveal their IP address to the other side or to third-party observers.
Although many developers had been a part of the Invisible IRC Project (IIP)[8] and Freenet communities, there are significant differences between their designs and concepts. IIP was an anonymous centralized IRC server. Freenet is a censorship-resistant distributed data store. I2P is an anonymous peer-to-peer distributed communication layer designed to run any traditional internet service (e.g. Usenet, email, IRC, file sharing, Web hosting and HTTP, Telnet), as well as more traditional distributed applications (e.g. a distributed data store, a web proxy network using Squid, or DNS).
Many developers of I2P are known only under pseudonyms. While the previous main developer, jrandom, is currently on hiatus,[9] others, such as zzz, killyourtv, and Complication have continued to lead development efforts, and are assisted by numerous contributors.[1]

I2P uses 2048bit ElGamal/AES256/SHA256+Session Tags encryption[10] and Ed25519EdDSA/ECDSAsignatures.[11]
Releases[edit]
I2P has had a stable release every six to eight weeks. Updates are distributed via I2P torrents and are signed by the release manager (generally zzz or str4d).
| I2P Versions | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
Software[edit]
Since I2P is an anonymous network layer, it is designed so other software can use it for anonymous communication. As such, there are a variety of tools currently available for I2P or in development.
The I2P router is controlled through the router console, which is a web frontend accessed through a web browser.
General networking[edit]
- I2PTunnel is an application embedded into I2P that allows arbitrary TCP/IP applications to communicate over I2P by setting up 'tunnels' which can be accessed by connecting to pre-determined ports on localhost.
- SAM (Simple Anonymous Messaging) is a protocol which allows a client application written in any programming language to communicate over I2P, by using a socket-based interface to the I2P router.[41]
- BOB (Basic Open Bridge) is a less complex app to router protocol similar to 'SAM'[42][43]
- Orchid Outproxy Tor plugin[44]
Chat[edit]
- Any IRC client made for the Internet Relay Chat can work, once connected to the I2P IRC server (on localhost).
File sharing[edit]
- Several programs provide BitTorrent functionality for use within the I2P network. Users cannot connect to non-I2P torrents or peers from within I2P, nor can they connect to I2P torrents or peers from outside I2P.[45]I2PSnark, included in the I2P install package, is a port of the BitTorrent client named Snark.[46]Vuze, formerly known as Azureus, is a BitTorrent client that includes a plugin for I2P, allowing anonymous swarming through this network.[47] This plugin is still in an early stage of development, however it is already fairly stable. I2P-BT is a BitTorrent client for I2P that allows anonymous swarming for file sharing. This client is a modified version of the original BitTorrent 3.4.2 program which runs on MS Windows and most dialects of Unix in a GUI and command-line environment. It was developed by the individual known as 'duck' on I2P in cooperation with 'smeghead'. It is no longer being actively developed; however, there is a small effort to upgrade the I2P-BT client up to par with the BitTorrent 4.0 release. I2PRufus is an I2P port of the Rufus BitTorrent client.[48]Robert (P2P Software) is the most actively maintained I2PRufus fork. XD is a standalone BitTorrent client written in Go.[49]
- Two Kad network clients exist for the I2P network, iMule and Nachtblitz. iMule (invisible Mule) is a port of eMule for I2P network. iMule has not been developed since 2013. iMule is made for anonymous file sharing. In contrast to other eDonkey clients, iMule only uses the Kademlia for proceeding to connect through I2P network, so no servers are needed. Nachtblitz[50] is a custom client built on the .NET Framework. The latest version is 1.4.27, released on March 23, 2016.[51] Nachtblitz includes a time lock to disable the software one year after its release date.
- I2Phex is a port of the popular Gnutella client Phex to I2P. It is stable and fairly functional.
- A port of Tahoe-LAFS has been ported to I2P. This allows for files to be anonymously stored in Tahoe-LAFS grids.
Bridging to Clearnet[edit]
Currently, Vuze is the only torrent client that makes clearnet (connections not through I2P) torrents available on I2P and vice versa, by using a plugin that connects them to the I2P network. Depending on the client settings, torrents from the internet can be made available on I2P (via announcements to I2P's DHT network) and torrents from I2P can be made available to the internet. For this reason, torrents previously published only on I2P can be made available to the entire Internet, and users of I2P can often download popular content from the Internet while maintaining the anonymity of I2P.[52][53]
Email[edit]
- I2P-Bote(github) is a free, fully decentralized and distributed anonymous email system with a strong focus on security.[54] It supports multiple identities and does not expose email metadata. As of 2015, it is still considered beta software. I2P-Bote is accessible via the I2P web console interface or using standard email protocols (i.e. IMAP/SMTP). All bote-mails are transparently end-to-end encrypted and signed by the sender's private key, thus removing the need for PGP or other email encryption software. I2P-Bote offers additional anonymity by allowing for the use of mail relays with variable length delays. Since it is decentralized, there is no centralized email server that could correlate different email identities as communicating with each other (i.e. profiling). Even the nodes relaying the mails do not know the sender, and apart from sender and receiver, only the end of the high-latency mail route and the storing nodes will know to whom (which I2P-Bote address – the user's IP address is still hidden by I2P) the mail is destined. The original sender could have gone offline long before the email becomes available to the recipient. No account registration is necessary, all you have to do in order to use it is create a new identity. I2P-Bote can be installed as an I2P plugin .[55]
- I2P also has a free pseudonymous e-mail service run by an individual called Postman. Susimail is a web-based email client intended primarily for use with Postman's mail servers, and is designed with security and anonymity in mind. Susimail was created to address privacy concerns in using these servers directly using traditional email clients, such as leaking the user's hostname while communicating with the SMTP server. It is currently included in the default I2P distribution, and can be accessed through the I2P router console web interface. Mail.i2p can contact both I2P email users, via user@mail.i2p and public internet email users from a user@i2pmail.org address.
- Bitmessage.ch can be used over I2P or Tor.
Instant Messaging[edit]
- I2P-Messenger is a simple Qt-based, serverless, end-to-end-encrypted instant messenger for I2P.[56] No servers can log the user's conversations. No ISP can log with whom the user chats, when, or for how long. As it is serverless, it can make use of I2P's end-to-end encryption, preventing any node between two parties from having access to the plain text. I2P-Messenger can be used for fully anonymous instant communication with persons the user doesn't even know, or, alternatively, to communicate securely and untraceably with friends, family members, or colleagues. In addition to messaging, file transfer is also supported.
- I2P-Talk is another simple instant messenger incompatible with I2P-Messenger, but having the same security properties
Publishing[edit]
- Syndie is a content distribution application, suitable for blogs, newsgroups, forums and small media attachments. Syndie is designed for network resilience. It supports connections to I2P, the Tor network (Syndie does not support Socks proxies, workaround needed for Tor access), Freenet and the regular internet. Server connections are intermittent, and support higher-latency communications. Connections can be made to any number of known servers. Content is spread efficiently using a Gossip protocol.
- Aktie is an anonymous file sharing and distributed Web of trust forums system. Aktie can connect to I2P with its internal router or use an external router. To fight spam, 'hash payments' (proof of CPU work) is computed for every published item.
Routers[edit]
- I2PBerry is a Linux distribution which can be used as a router to encrypt and route network traffic through the I2P network.
- i2pd is a light-weight I2P router written in C++, stripping the excessive applications such as e-mail, torrents, and others that can be regarded as bloat.[57][58]
- Kovri is an I2P router written in C++.[59] It was forked from i2pd following developer disagreements.[60] Kovri's primary purpose is to integrate with the cryptocurrency Monero to send new transaction information over I2P, making it much more difficult to find which node is the origin of a transaction request.[61] Those using the Kovri router will be running full I2P routers that contribute to the I2P network the same way the current Java router does. This project is expected to benefit both the Monero and I2P communities, since it will allow for greater privacy in Monero, and it should increase the number of nodes on the I2P network.[62]
The Privacy Solutions project[edit]
The Privacy Solutions project,[63] a new organization that develops and maintains I2P software, launched several new development efforts designed to enhance the privacy, security, and anonymity for users, based on I2P protocols and technology.
These efforts include:[64]
- The Abscond browser bundle.
- i2pd,[65] an alternate implementation of I2P, written in C++ (rather than Java).
- The 'BigBrother' I2P network monitoring project.
The code repository and download sections for the i2pd and Abscond project is available for the public to review and download.[66]Effective January, 2015 i2pd is operating under PurpleI2P.[67]
Android[edit]
- Release builds of an I2P Router application for Android can be found on the Google Play store under The Privacy Solutions Project's Google Play account or on an F-Droid repository hosted by the developers.[68]
- Nightweb is an Android application that utilizes I2P and Bittorrent to share blog posts, photos, and other similar content. It can also be run as a desktop application. It is no longer in development.[69]
Crypto-Currency[edit]
Some crypto currencies that support I2P are listed below.
Terminology[edit]
I2p Browser Download
- Eepsite
- Eepsites are websites that are hosted anonymously within the I2P network. Eepsite names end in .i2p, such as ugha.i2p or forum.i2p. EepProxy can locate these sites through the cryptographic identifier keys stored in the hosts.txt file found within the I2P program directory. Typically, I2P is required to access these eepsites.[71]
- .i2p
- 'I2p' is a pseudo-top-level domain which is only valid within the I2P overlay network scope. .i2pnames are resolved by browsers by submitting requests to EepProxy which will resolve names to an I2P peer key and will handle data transfers over the I2P network while remaining transparent to the browser.[72]
- EepProxy
- The EepProxy program handles all communication between the browser and any eepsite. It functions as a proxy server that can be used by any web browser.
- Peers, I2P nodes
- Other machines using I2P that are connected to user's machine within the network. Each machine within the network shares the routing and forwarding of encrypted packets.
- Tunnels
- Every ten minutes, a connection is established between the user's machine and another peer. Data to and from the user, along with the data for other peers (routed through the user's machine), pass through these tunnels and are forwarded to their final destination (may include more jumps).[73]
- netDb
- The distributed database that holds information on I2P nodes and I2P eepsites. This database is split up among routers known as 'floodfill routers'. When a user wants to know how to contact an eepsite, or where more peers are, they query the database.[74]
I2PCon[edit]
From August 15, 2015 to August 16, 2015 the first I2P convention was held in Toronto, Ontario.[75] The conference was hosted by a local hackerspace, Hacklab. The conference featured presentations from I2P developers and security researchers.
August 15, 2015 mainly had presentations on the past growth of the I2P network, a talk on what happens when companies sell people's personal information, and a round-table discussion on general privacy and security topics. The day ended with a CryptoParty, which helped to introduce new users to installing I2P, sending secure emails with I2P-Bote, and using I2P along with Vuze.
August 16, 2015 had more technical discussions than the previous day. The talks focused what how to dissuade bad-actors from using the network, how I2P has worked computer connection limits, how to do application development using I2P, and the development of the Android version. This day ended with a development meeting.
Cultural references[edit]
In House of Cards Season 2 Episode 2, I2P is referenced.[76]
See also[edit]
Software[edit]
References[edit]
- ^ ab'I2P Project Members'. geti2p.net. Retrieved 22 November 2015.
- ^ ab'0.9.39 Release'. geti2p.net.
- ^I2P (project), Transifex.
- ^'Licenses', Get involved, Get I2P.
- ^Get I2P (blog).
- ^'Benefits of Tor over I2P'. I2P Dev Team. Retrieved 23 December 2013.
- ^'Garlic Routing - I2P'. geti2p.net.
- ^'IIP', Invisible IP, Source forge.
- ^'Jrandom's Announcement - I2P'. geti2p.net. Retrieved 2017-07-15.
- ^'ElGamal/AES + SessionTag Encryption - I2P'. geti2p.net.
- ^'Crypto/ECDSA – I2P Bugtracker'. trac.i2p2.de.
- ^zzz (8 February 2014). '0.9.11 Release'. geti2p.net.
- ^zzz (31 March 2014). '0.9.12 Release'. geti2p.net.
- ^zzz (22 May 2014). '0.9.13 Release'. geti2p.net.
- ^zzz (26 July 2014). '0.9.14 Release'. geti2p.net.
- ^zzz (9 August 2014). '0.9.14.1 Release'. geti2p.net.
- ^zzz (20 September 2014). '0.9.15 Release'. geti2p.net.
- ^zzz (1 November 2014). '0.9.16 Release'. geti2p.net.
- ^zzz (30 November 2014). '0.9.17 Release'. geti2p.net.
- ^zzz (22 February 2015). '0.9.18 Release'. geti2p.net.
- ^zzz (12 April 2015). '0.9.19 Release'. geti2p.net.
- ^zzz (2 June 2015). '0.9.20 Release'. geti2p.net.
- ^zzz (31 July 2015). '0.9.21 Release'. geti2p.net.
- ^zzz (12 December 2015). '0.9.22 Release'. geti2p.net.
- ^str4d (19 November 2015). '0.9.23 Release'. geti2p.net.
- ^zzz (27 January 2016). '0.9.24 Release'. geti2p.net.
- ^zzz (3 March 2016). '0.9.25 Release'. geti2p.net.
- ^zzz (7 June 2016). '0.9.26 Release'. geti2p.net.
- ^zzz (17 October 2016). '0.9.27 Release'. geti2p.net.
- ^zzz (12 December 2016). '0.9.28 Release'. geti2p.net.
- ^zzz (27 February 2017). '0.9.29 Release'. geti2p.net.
- ^zzz (3 May 2017). '0.9.30 Release'. geti2p.net.
- ^zzz (7 August 2017). '0.9.31 Release'. geti2p.net.
- ^zzz (11 November 2017). '0.9.32 Release'. geti2p.net.
- ^zzz (30 January 2018). '0.9.33 Release'. geti2p.net.
- ^zzz (10 April 2018). '0.9.34 Release'. geti2p.net.
- ^zzz (26 June 2018). '0.9.35 Release'. geti2p.net.
- ^zzz (23 August 2018). '0.9.36 Release'. geti2p.net.
- ^zzz (4 October 2018). '0.9.37 Release'. geti2p.net.
- ^zzz (22 January 2019). '0.9.38 Release'. geti2p.net.
- ^'SAM', API, I2P.
- ^'BOB', API, Get I2P.
- ^BOB: Basic Open Bridge API to the I2P router (official eepsite), archived from the original on 2015-12-04.
- ^'Contribute to subgraph/Orchid development by creating an account on GitHub'. 7 March 2019 – via GitHub.
- ^I2P Bittorrent FAQ (forum), DE: i2p2, archived from the original on 2011-11-03.
- ^The Hunting of the Snark Project – BitTorrent Application Suite, Klomp.
- ^'How To for I2P Network Plugin', I2PHelper(Howto) (setup tutorial), Vuze.
- ^'Rufus – BitTorrent Client'. Sourceforge..
- ^'i2p bittorrent client. Contribute to majestrate/XD development by creating an account on GitHub'. 22 March 2019 – via GitHub.
- ^Official Nachtblitz Resource, nachtblitz
- ^'i2p.xyz - Informationen zum Thema i2p'. echelon.i2p.xyz.
- ^'Vuze Speeds Up Torrent Downloads Through 'Swarm Merging''. TorrentFreak. 20 March 2015. Retrieved 4 June 2016.
- ^'I2PHelper HowTo'. VuzeWiki. Retrieved 4 June 2016.
- ^I2P-Bote, I2P, archived from the original on 2015-09-13.
- ^Plugins, I2P, archived from the original on 2015-09-09
- ^Introducing I2P, Nov 10, 2015
- ^'PurpleI2P/i2pd'. GitHub. Retrieved 2018-08-20.
- ^'Invisible Internet Protocol Daemon'. i2pd.website. Retrieved 2018-08-20.
- ^https://getkovri.org/index.html[dead link]
- ^'What is the difference between i2pd and Kovri?'. StackExchange. Retrieved 4 March 2017.
- ^'Kovri - Moneropedia'. GetMonero. Retrieved 4 March 2017.
- ^'What use cases will Kovri have for Monero?'. StackExchange.
- ^Privacy Solutions project.
- ^List of ongoing Privacy Solutions projects.
- ^'Invisible Internet Protocol Daemon'. i2pd.website.
- ^Active development, The Privacy Solutions
- ^Active development, Purple I2P
- ^Android App Releases
- ^Discontinued, Nightweb.
- ^'I2P con 2015 - Growing the Network, Spreading the Word, 03:41'. YouTube.
- ^'Intro'. I2P. Retrieved 4 June 2016.
- ^'Naming and Addressbook - I2P'. geti2p.net. Retrieved 4 June 2016.
- ^'Tunnel Routing'. I2P. Retrieved 4 June 2016.
- ^'The Network Database'. I2P. Retrieved 4 June 2016.
- ^'I2PCon: Mission Accomplished - Blog'. I2P. Retrieved 4 June 2016.
- ^'Hacker-Turned-Consultant Helps 'House Of Cards''. New Orleans Public Radio. 9 April 2014. Retrieved 4 October 2017.
External links[edit]
- Official website
How To Download Torrent With I2p Windows 10
